The stability of global energy markets and the integrity of Western IT infrastructure now hinge on a fragile calculus of "Escalation Dominance." Iran’s recent threats to target U.S. and allied energy and information systems—contingent upon an Israeli or American strike on Iranian oil fields—represents more than mere rhetoric. It is a calculated application of asymmetric warfare designed to equalize a conventional military deficit. By positioning the global economy as a hostage to regional kinetic action, Tehran utilizes a defensive doctrine predicated on "Vertical Escalation," where the response to a localized physical strike is a diversified, cross-domain counter-strike intended to trigger systemic failure.
The Architecture of Asymmetric Deterrence
Iran’s strategic posture is defined by three distinct operational pillars. Each pillar serves to offset the technical and conventional superiority of its adversaries by exploiting the inherent vulnerabilities of interconnected global systems.
- The Energy Chokepoint (Kinetic and Tactical): This involves the physical disruption of maritime transit via the Strait of Hormuz and targeted strikes on regional production facilities (e.g., Aramco's Abqaiq-Khurais).
- The Information System Vector (Cyber-Offensive): Utilizing Advanced Persistent Threats (APTs) to penetrate Supervisory Control and Data Acquisition (SCADA) systems within U.S. utility and IT sectors.
- The Proxy Multiplier: The use of non-state actors (Hezbollah, Houthis, PMF) to execute deniable strikes, thereby complicating the "Attribution-Response" cycle for Western decision-makers.
The core objective is not to win a conventional war, which Iran recognizes as an impossibility, but to make the cost function of a Western strike prohibitively high. If the cost of an Israeli strike on the Kharg Island oil terminal is measured in $300-per-barrel oil and a collapse of the U.S. banking cloud, the strategic utility of that strike vanishes.
Quantifying the Vulnerability of Global Energy Loops
The threat to "fuel sectors" is often discussed in vague terms of supply and demand. A rigorous analysis requires breaking down the energy supply chain into its critical nodes: Extraction, Refinement, and Distribution.
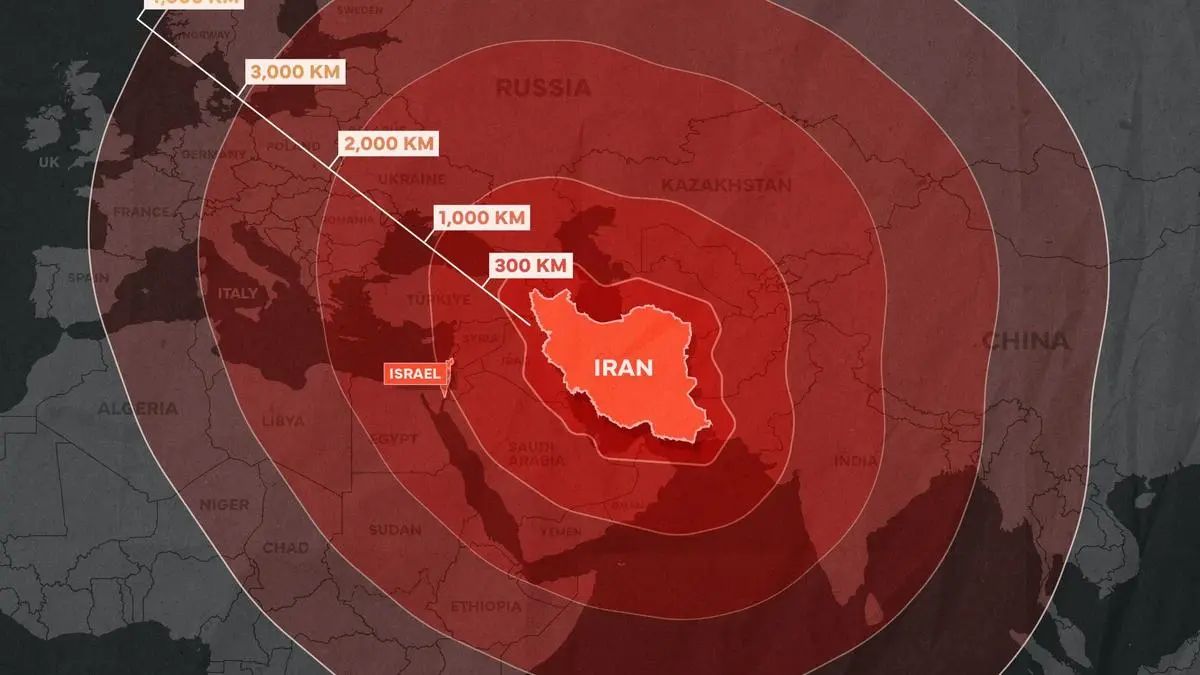
Iran's threat focuses on the Distribution Node. The Strait of Hormuz remains the most significant oil transit chokepoint globally, with approximately 20-21 million barrels per day (bpd) of crude and products passing through—roughly 20% of global consumption. Unlike a temporary supply shock, a disruption here creates a "Liquidity Trap" in the energy market. Physical oil cannot be rerouted quickly enough to prevent a price spike.
The Cost Function of Maritime Blockades
The economic impact of a disruption in the Persian Gulf is governed by the Elasticity of Supply. In the short term, supply is perfectly inelastic; refineries cannot immediately switch to alternative grades of crude, and strategic reserves (SPR) have limited discharge rates.
- Primary Effect: Immediate 30-50% surge in Brent and WTI futures based on risk-premium pricing.
- Secondary Effect: A catastrophic rise in "War Risk" insurance premiums for tankers, effectively halting shipping even in areas not directly under fire.
- Tertiary Effect: Inflationary pressure on global logistics, as the cost of bunker fuel drives up the price of all containerized goods.
The Cyber-Physical Interface: Threatening the IT Core
Tehran’s threat to "IT systems" is a shift from traditional espionage to Destructive Cyber Operations (DCO). While previous Iranian campaigns focused on data exfiltration or Distributed Denial of Service (DDoS) attacks against banks (e.g., Operation Ababil), the current doctrine emphasizes the "Cyber-Physical" crossover.
SCADA and ICS Vulnerabilities
The most significant risk lies in the compromise of Industrial Control Systems (ICS). Many U.S. energy utilities and water treatment plants operate on legacy SCADA systems that were never designed for the internet-facing environment.
The mechanism of a destructive attack follows a specific lifecycle:
- Reconnaissance: Identifying internet-connected Human-Machine Interfaces (HMIs).
- Access and Persistence: Deploying "wiper" malware (such as Shamoon or its derivatives) to erase hard drives and render hardware unbootable.
- Kinetic Triggering: Manipulating pressure valves or electrical frequency regulators to cause physical damage to turbines, transformers, or pipelines.
This creates a "Duration Gap." While a DDoS attack can be mitigated in hours, a successful strike on a physical transformer can take months to repair due to lead times in the global manufacturing supply chain for high-voltage equipment.
The Logical Framework of Iranian Escalation
To understand why Iran believes this threat is credible, we must examine the Rational Actor Model under duress. Iran perceives its oil infrastructure as its "Center of Gravity." If this center is neutralized, the regime loses its primary source of hard currency and domestic stability.
In this scenario, "Proportionality" ceases to be a constraint. The Iranian high command likely operates under a Total Loss Threshold. If the regime believes its survival is at stake due to the destruction of its energy sector, it has no incentive to remain within the bounds of "calibrated" responses. This leads to what game theorists call a "Grim Trigger" strategy: any strike on Node A (Iranian Oil) results in a permanent and total offensive against Node B (Global Energy/IT).
The Attribution Dilemma
A key component of this strategy is the ambiguity of the "Aggressor’s Identity." By utilizing proxy groups or sophisticated cyber tools that mimic other actors, Iran can execute its threat while maintaining a degree of plausible deniability. This creates a bottleneck in the Western response loop. If a U.S. utility goes offline due to a cyberattack, the time required for forensic attribution (often weeks or months) provides Iran with a window to negotiate from a position of strength before a retaliatory strike is authorized.
Critical Weaknesses in the Iranian Strategy
While the threat is formidable, it is not without structural flaws. The "Maximum Pressure" logic assumes that the global community will blame the initial aggressor (Israel or the U.S.) rather than the retaliator (Iran). This is a significant miscalculation for two reasons.
- The China Variable: China is the primary consumer of Iranian crude. If Iran shuts down the Strait of Hormuz or causes a global energy spike, it directly sabotages the economy of its most important geopolitical partner. This creates a diplomatic ceiling on how far Tehran can actually go.
- Hardened Resilience: Since the 2012 attacks on Saudi Aramco and the Sands Casino, Western IT infrastructure has undergone significant "Hardening." Air-gapping critical systems and the implementation of Zero Trust Architecture (ZTA) have made "widening" attacks—those that spread across an entire network—significantly more difficult to execute.
Strategic Realignment for Infrastructure Defense
Mitigating this threat requires moving beyond reactive defense toward Antifragile Systems. This involves a shift in how energy and IT sectors are managed during periods of high geopolitical tension.
Decentralization of the Energy Grid
The vulnerability of centralized IT systems is exacerbated by the centralization of power generation. Transitioning to a distributed microgrid model reduces the "Blast Radius" of a cyber-physical attack. If one node is compromised, the rest of the grid remains operational.
Active Cyber Defense (ACD)
Instead of waiting for an intrusion, organizations must employ "Threat Hunting" protocols. This involves proactively searching for indicators of compromise (IoCs) within the network, specifically looking for lateral movement patterns typical of Iranian APTs like "OilRig" or "Rocket Kitten."
Strategic Petroleum Reserve (SPR) Optimization
The SPR should not be viewed as a price-control tool, but as a "Strategic Buffer" against kinetic disruption. Policy must prioritize the readiness of the SPR to offset a total Hormuz blockage for a minimum of 90 days, providing the necessary window for military or diplomatic resolution without immediate domestic economic collapse.
The Operational Reality of Cross-Domain Conflict
The current standoff is not a precursor to a standard regional war; it is the first major test of "Integrated Deterrence." The U.S. and its allies are facing a situation where the front line is not a border, but a server room in Virginia or a pumping station in the Eastern Province of Saudi Arabia.
The threat is credible because the tools required—ballistic missiles, drones, and malware—are inexpensive compared to the systems they target. This Negative ROI for Defense means that for every $1 Iran spends on an offensive drone or a piece of wiper malware, the U.S. must spend $1,000 in air defense or cybersecurity remediation.
The strategic play for Western powers is to decouple their critical infrastructure from the "Escalation Ladder." This means ensuring that a strike in the Middle East does not have a "Short Circuit" path to the domestic economy. Achieving this requires a rigorous, data-driven audit of every point where the global energy market touches the digital world. Only by eliminating these "Single Points of Failure" can the threat of asymmetric retaliation be neutralized.
The immediate priority for IT and energy executives is the execution of a "Disconnected State" drill: can your operations survive a 72-hour total loss of external connectivity and a 100% increase in fuel costs? If the answer is no, the vulnerability is not Iranian intent, but internal systemic fragility.
Would you like me to analyze the specific malware signatures historically associated with Iranian APTs to help refine your threat-hunting protocols?