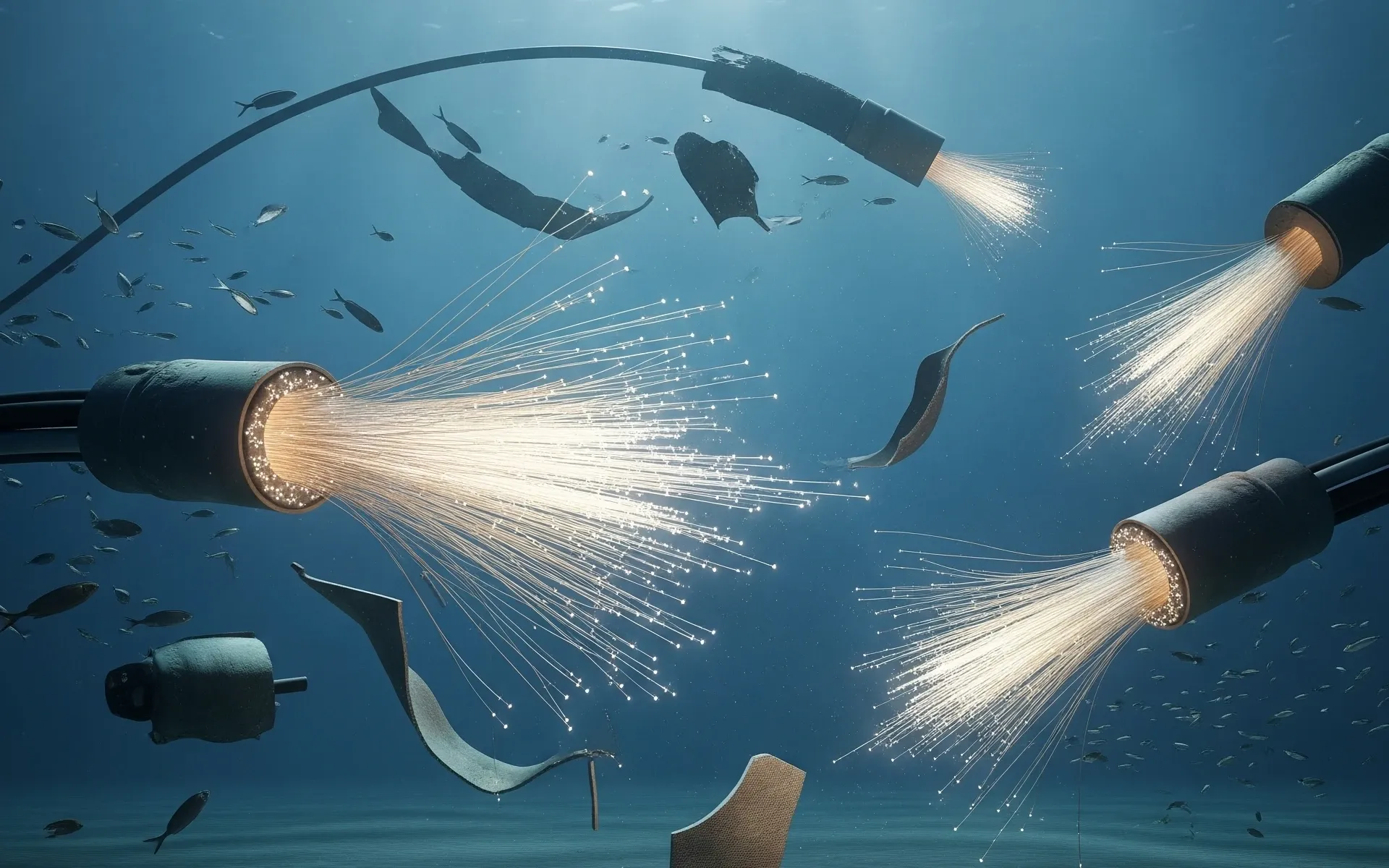
The narrative surrounding the Persian Gulf is currently obsessed with a ghost story. Security analysts are falling over themselves to warn about Iran’s IRGC targeting undersea fiber-optic cables and cloud networks. They paint a picture of a global digital blackout triggered by a single well-placed anchor or a specialized mini-sub. It is a terrifying, cinematic, and fundamentally flawed premise.
If you believe that snipping a cable in the Strait of Hormuz "disconnects" the West or even cripples regional digital infrastructure, you don't understand how the internet actually functions. You are falling for a geopolitical bluff that ignores the physics of data routing and the brutal reality of economic suicide. For a deeper dive into similar topics, we recommend: this related article.
The Redundancy Myth That Refuses to Die
Most breathless reports on "cable vulnerability" treat the internet like a garden hose. They assume that if you kinking the hose, the water stops. In reality, the global subsea network is a high-density mesh.
There are currently over 550 active and planned undersea cables globally. In the Middle East alone, the redundancy is staggering. If a cable in the Persian Gulf is severed, BGP (Border Gateway Protocol)—the internet’s post office—automatically reroutes traffic through terrestrial links across Egypt, satellite constellations, or alternative paths through the Mediterranean. For additional context on this issue, in-depth reporting can be read at Al Jazeera.
Will latency spike? Perhaps by 40 milliseconds. Will the world stop spinning? Not even close.
I have watched Tier-1 providers handle simultaneous triple-fiber cuts in the Atlantic without the average user noticing a single dropped Zoom call. The "digital apocalypse" scenario assumes a fragility that died in the late 1990s. When the IRGC "flags" these as targets, they aren't threatening a knockout blow; they are threatening a minor inconvenience that costs more to execute than it's worth.
Why Iran Cannot Afford to Win This Fight
Here is the data point the "security experts" conveniently omit: Iran is just as dependent on these "targets" as their adversaries.
The IRGC's own financial interests, their domestic surveillance apparatus, and their ability to sell oil through shadow markets all rely on the same regional cloud nodes and subsea hops they are supposedly threatening.
- Digital Sovereignty vs. Economic Reality: Iran’s "National Information Network" (NIN) is an attempt to decouple from the global web, but it’s a shell. It still relies on peering points in Muscat, Dubai, and Istanbul.
- The Cloud Paradox: Threatening cloud networks in the UAE or Saudi Arabia is effectively threatening the backup servers for Iranian state-linked businesses.
- The Insurance Suicide: Undersea cables are mostly owned by private consortia, not governments. Cutting them invites the wrath of global insurance syndicates and private capital from China and India—Iran’s only remaining economic lifelines.
Imagine a scenario where the IRGC cuts the FLAG (Fiber-optic Link Around the Globe) cable. They wouldn't just be "hitting the West." They would be disconnecting the very Chinese financial systems they use to bypass US sanctions. It is a strategic non-starter.
The Cloud is Not a Building You Can Bomb
The competitor article suggests "cloud networks" are at risk. This reveals a deep misunderstanding of distributed computing.
You cannot "blow up" the cloud. You can blow up a data center. But the entire architecture of AWS, Azure, and Google Cloud in the Middle East is built on Availability Zones (AZs). Data is mirrored across multiple physical locations with independent power and cooling.
To take down a regional cloud network, you would need a coordinated kinetic strike on a dozen hardened facilities simultaneously. If a nation-state reaches the point where they are launching swarm drones at twenty different air-conditioned warehouses in Riyadh and Dubai, we aren't in a "digital threat" anymore. We are in World War III. At that point, your Instagram feed being down is the least of your problems.
The Real Threat is Not Kinetic
Stop looking at the seabed. The obsession with physical cable-cutting is a distraction from the actual theater of war: the management layer.
If I wanted to disrupt the Persian Gulf’s digital economy, I wouldn't waste money on a submarine. I would go after the Network Management Systems (NMS). The software that controls the optical amplifiers and the routing tables is far more vulnerable than the physical glass on the ocean floor.
A state-sponsored actor doesn't need to break a cable; they need to compromise the firmware of the routers that light that cable. That is where the IRGC actually spends its budget. They don't want to break the internet; they want to own the data flowing through it. Physical destruction is for amateurs. Strategic infiltration is for pros.
The "People Also Ask" Delusions
Let’s address the standard questions that pop up in every panicked boardroom:
"Are undersea cables protected by international law?" Yes, but international law is a polite suggestion during a conflict. The real protection is the UNCLOS (United Nations Convention on the Law of the Sea), which protects the right to lay cables. But the actual protection is the $500 million price tag of a repair ship. No one wants to pay for it, which creates a "mutually assured disruption" pact.
"Can a single sub-surface drone take down the internet?" No. Period. You would need a fleet working in perfect synchronization across multiple choke points—the Bab-el-Mandeb, the Strait of Hormuz, and the Suez Canal—to cause more than a localized outage.
"What about satellite internet as a backup?" Starlink and its competitors are the ultimate counter-argument to IRGC cable threats. The moment a physical cable is cut, traffic shifts to the sky. The "bottleneck" strategy only works if there are no other exits. In 2026, there are exits everywhere.
The Cost-Benefit Failure
The IRGC thrives on asymmetrical warfare. They want maximum fear for minimum investment.
Operating a deep-sea intervention team is expensive, technically difficult, and high-risk. If a diver is caught 200 meters down near a cable, the attribution is immediate. The retaliation would be devastating.
Contrast that with a cyber-attack on a regional bank’s SWIFT gateway. It’s cheaper, anonymous, and far more disruptive to the "fragile economy" the media keeps talking about.
The focus on undersea cables is "security theater." It looks good on a PowerPoint slide and makes for a scary headline, but in the hierarchy of actual risks, it ranks somewhere below a botched software update from a major vendor.
The Hard Truth
We need to stop treating every IRGC press release as a viable military strategy. Their "flagging" of undersea cables is a psychological operation, not a tactical one. They are counting on the fact that most Westerners think the internet comes from the air and is easily broken by a man with a pair of bolt cutters.
It’s not. The internet is the most resilient machine ever built by man. It was designed to survive a nuclear exchange, not just a disgruntled regional power with a few divers.
The next time you see a headline about "threats to undersea infrastructure," ignore the cable. Look at the software. Look at the routing tables. Look at the people who control the keys to the encryption. Everything else is just noise for the uninitiated.
The IRGC isn't going to cut the cables because they know something the media doesn't: they'd be the ones left in the dark.