The headlines are exactly what the intelligence apparatus wants you to see. They scream about "links," "coordination," and "direct chains of command" between a high-ranking Hezbollah commander and a specific attacker at a Michigan synagogue. It is a neat, cinematic narrative. It suggests a world where a puppeteer in Beirut pulls a string and a window breaks in Detroit.
It is also a profound misunderstanding of how modern asymmetrical warfare actually functions.
By hyper-focusing on the "commander" at the top of the press release, we are ignoring the far more terrifying reality of the decentralized, "gig economy" version of global terror. The IDF and domestic agencies are playing a 1990s game of Connect-the-Dots while the adversary has moved to a serverless, cloud-based architecture.
The Myth of the Puppet Master
The competitor narrative relies on a vertical hierarchy. They want you to believe that if you identify the commander, you have "solved" the threat. This is a comfort blanket for the public and a budget-booster for agencies. If there is a boss, there is a target. If there is a target, there is a mission.
In reality, the relationship between Lebanese leadership and a domestic actor is rarely a straight line. It is a murky, overlapping Venn diagram of shared grievances, encrypted Telegram channels, and "inspirational" radicalization.
When the IDF links a specific name to a specific crime in Michigan, they are often performing a post-hoc forensic squeeze. They find a digital footprint—a shared server, a common contact in a third country, a crypto-wallet transfer—and they call it a "command structure." I have seen analysts spend months trying to prove a direct order existed when the truth was much simpler: the attacker was a self-starting freelancer seeking validation from a brand name they admired.
The Intelligence Trap: Confusing Correlation with Command
Why does this distinction matter? Because if you treat a decentralized threat like a traditional army, you fail to stop the next one.
When we tell the public that an "attacker was linked to a commander," we imply that by monitoring known commanders, we can prevent attacks. This is a lie of omission. Modern radicalization works through Stochastic Terrorism. This isn’t a complex variable in a $LaTeX$ equation; it is basic probability. You broadcast a signal to a million people, and statistically, one of them will be unstable enough to act.
The "commander" didn't need to send an email. They just needed to exist as a symbol.
- The Competitor View: The commander sent an operative.
- The Reality: The environment created a vacuum, and a local actor filled it using the commander's "brand" as a blueprint.
By focusing on the "link," we ignore the infrastructure of radicalization—the platforms, the dark-web exchanges, and the local radicalization pipelines that operate entirely independently of any Middle Eastern general.
The Michigan Connection: Why "Who" is the Wrong Question
People are asking, "How did a Hezbollah commander reach into Michigan?" They should be asking, "Why is Michigan’s digital and social landscape so permeable to this specific brand of influence?"
Michigan has become a focal point for this discussion not because it is crawling with foreign spies, but because it is a microcosm of the West's failure to police its own digital borders. We are obsessed with the foreign "entity" because it’s easier to blame an external bogeyman than to admit that our own technological platforms have made geographical distance irrelevant.
In my years tracking these movements, I’ve watched agencies celebrate the "neutralization" of a mid-level coordinator, only for three more to pop up the next day. Why? Because the coordinator wasn’t the source of the energy; they were just the lightning rod.
The High Cost of the "Link" Narrative
There is a dark side to this obsession with proving direct links. It leads to Security Theater.
When the news cycle focuses on a specific commander, resources are shifted toward "high-value targets." We spend billions on drone strikes and international wiretaps. Meanwhile, the "low-level" threats—the guys buying components at a local hardware store after watching a three-minute video—slip through the cracks.
- Over-Classification: By claiming "secret intel" links the two, agencies avoid showing their work. They ask for trust they haven't earned.
- Resource Misallocation: We hunt for a general while the foot soldiers are recruiting in plain sight on Discord.
- Diplomatic Friction: Using local crime to justify foreign military policy creates a feedback loop that rarely results in actual domestic safety.
The Digital Ghost in the Machine
We need to stop talking about "Hezbollah in Michigan" as if it’s a troop deployment. It is a franchise model.
Think of it like a fast-food chain. The corporate office (Beirut) provides the "recipes" (ideology and tactics) and the "branding." The local owner (the Michigan attacker) provides the capital, the location, and the labor. Corporate doesn't need to know the guy flipping the burgers. They just need him to follow the manual.
If you want to stop the "attacker," you don't just go after the CEO in Lebanon. You have to make the "recipe" impossible to distribute and the "brand" toxic to hold.
Stop Asking "Who" and Start Asking "How"
The "People Also Ask" sections of the internet are filled with queries about the commander’s name, his history, and his rank. These are the wrong questions. They are trivia.
The brutal honesty is this: the commander's identity is irrelevant to your safety. What is relevant is the latency of response. How long does it take for a digital signal sent from a bunker in the Levant to manifest as a physical threat in the American Midwest?
Current estimates suggest that the window from "radicalization" to "action" has shrunk by over 70% in the last decade. This isn't because the commanders got smarter. It's because the friction of communication has been erased.
The Counter-Intuitive Truth
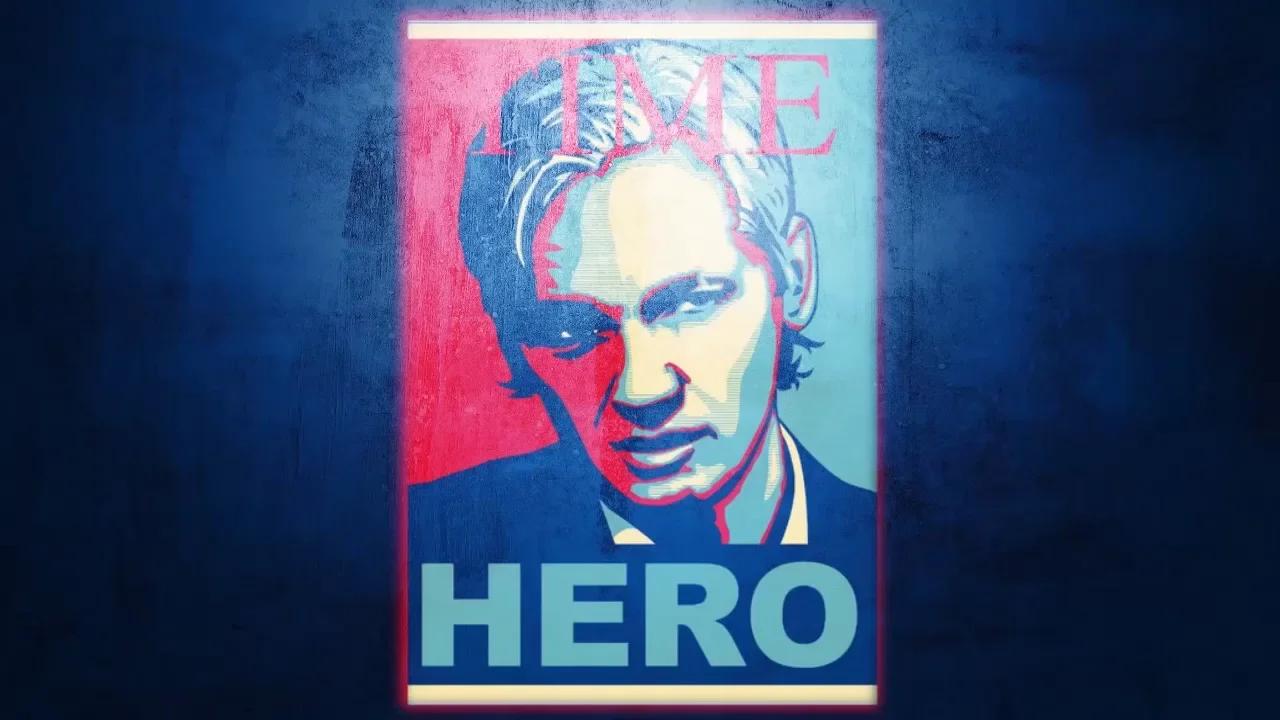
If we actually wanted to dismantle this threat, we would stop making these commanders famous. Every time a major news outlet puts a Hezbollah leader’s face next to a domestic attack, they are providing that organization with free "proof of concept" marketing. They are telling every other potential lone wolf: "Look what this guy can help you achieve. You can be part of a global movement."
We are effectively doing their recruiting for them by validating their reach.
The most effective way to handle these "links" is to treat the domestic attacker as a common, pathetic criminal and the foreign commander as a distant, failing bureaucrat. Instead, we give them the "Mastermind" treatment. It’s an ego-stroke that fuels the next cycle.
The Intelligence Industrial Complex
The IDF’s insistence on this link is also a geopolitical tool. By tying domestic US threats to Hezbollah, they ensure continued US backing for their own regional operations. It’s a "you scratch my back, I’ll protect your synagogues" arrangement.
While the threats are real, the presentation of the data is curated to serve a specific policy goal. I have seen intelligence reports where "possible association" becomes "confirmed coordination" by the time it reaches the press office. This isn't a conspiracy; it's just how the bureaucracy of war operates. They need the threat to be organized because you can't fight a "vibe" with a billion-dollar missile defense system.
You have to turn the "vibe" into a "commander."
The Michigan attacker likely didn't have a direct line to a general. He had a browser, a grievance, and an ecosystem that told him he was a soldier. Until we address the ecosystem, the commanders are just names on a list, and the "links" are just ghosts we're chasing while the house burns down.
Stop looking for the general. Start looking at the mirror of our own digital negligence.
Go look at your own local community’s digital resilience. If you think a commander in Beirut is the primary reason for a domestic security breach, you’ve already lost the war of information. You're waiting for a ship to dock when the virus is already in the water supply.